#EnhancedConnectivity – Data logging and data transformation
Lecture
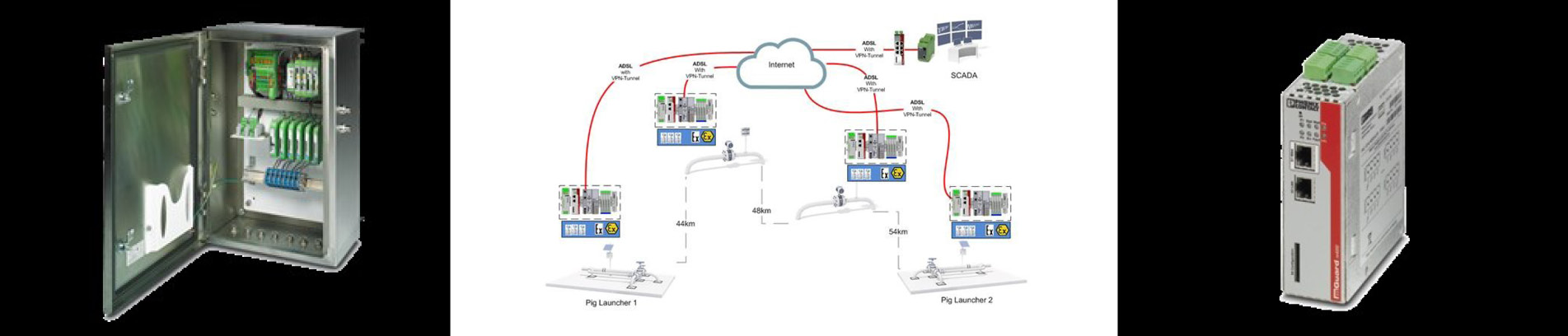
Key of the optimization of processes and monitoring them is data. The data needs to be collected, transferred to central control rooms and more than anything else – data and the systems need to be protected from cyber-attacks. Phoenix Contact has realized plenty of projects in the field of data logging and transformation of data – also in cooperation with Krohne. Concepts here shall be demonstrated by means of a pipeline monitoring and leakage detection system. Here and in many more similar projects Krohne delivered the sensors and the calculation tools in a central control room. Phoenix Contact provided data logging systems and concepts to bring the data to the control room including the relevant time stamps so the monitoring of the pipeline and the detection of leakages including their position could be realized by Krohne. Here the necessary firewalls from PhoenixContact have always been part of the solution.
Key Takeaways
- Why do I need data logging and data transmission in a monitoring solution
- What are the different concepts of data transfer
- How does a Phoenix Contact solution look like
- How did Phoenix Contact realize such a system in a pipeline monitoring project in co-operation with Krohne
- Cyber security in these systems – why do I need it and what can Phoenix Contact offer